What can go wrong with a tool that just logs messages to a text-based file? Nothing right? Suddenly on December 11, 2021, we were all exposed to the log4j vulnerability, and your organization could have been (might have been?) breached!
A quick definition of what Log4j is
The software industry has become increasingly reliant on reusable code—software libraries—to reduce development time and cost. Log4j is a widely used library written in Java under the Apache Software License. It provides developers with an effective way to track and monitor the activity of their applications and services. Its use helps ensure reliable, user-friendly software.
Log4j Vulnerability Explained
Log4j is an extremely popular and heavily used open-source Java library that can be used for unauthenticated remote code execution, making CVE-2021-44228 and CVE-2021-45046 critical vulnerabilities that you must pay attention to.
In other words: if your software uses this library, then there is a good chance that anyone can gain full remote control of your servers and data.
The log4j vulnerability is among the worst we’ve seen in the last 5 years, in part because the vulnerability itself is so severe and so easy to trigger. It allows anyone with access to the network or internet to gain unauthorized access to data. Adding to the severity, this vulnerable library is among the most popular and widely deployed open-source Java libraries on the planet.
Differences between log4j vulnerability versions?
The Apache Struts disaster from 2017 (CVE-2017-5638) was a large part of why we launched our startup (MergeBase): to help companies protect themselves from known vulnerabilities in open source libraries exactly like these.
This time it’s even worse. This particular vulnerability is especially dangerous because it can be exploited remotely without the need for authentication. This means that attackers can easily target systems that are using vulnerable versions of log4j and can potentially gain full control over them.
Globally, everyone must now urgently scramble to upgrade all applicable software to use Java library log4j version at least 2.15.0 (which was published today). Companies that, for whatever reason, fail to execute this upgrade will likely be attacked and exploited within the next few days – assuming they are not already under attack.
We cannot stress how urgent it is for administrators of Java systems to succeed in rolling out this upgrade. Patch this Critical log4j vulnerability in Java CVE-2021-44228 immediately.
How can you check for vulnerabilities?
There is an easy way to check any server for the log4j vulnerability. At the root of your file system, using an administrator account, download and run our free Log4J-Detector tool.
This command can take several hours to complete. Any occurrence of “_VULNERABLE_” in this command’s output indicates with a high probability that you are vulnerable to this severe software exploit.
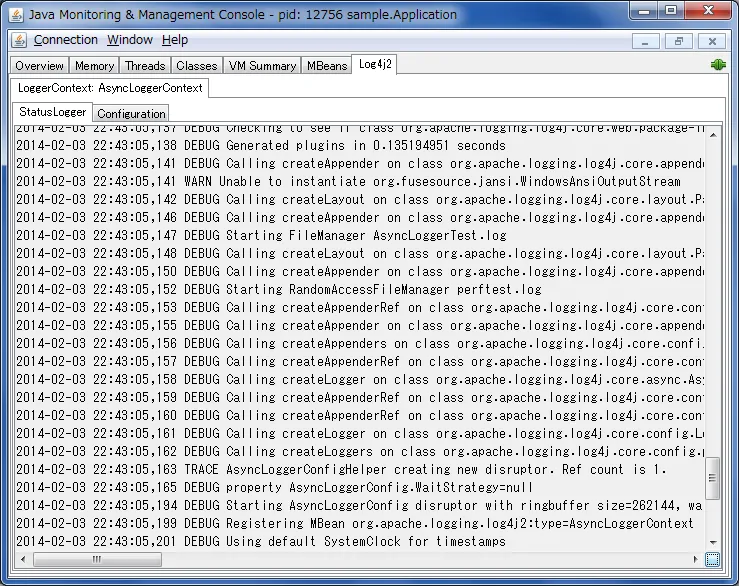
Monitoring - Log4J Vulnerability
Further reading:
- LunaSec
- The Cybersecurity and Infrastructure Security Agency has issued a guide that gives assistance in scanning internet-facing assets and prioritizing patching. The guide also makes suggestions for monitoring for unusual traffic that could be an indication of attempted exploitation of the Log4j vulnerability.
Still interested in learning more about it?
Check the video on securing log4j instantly with Dynamic Application Surveillance and Hardening.
MergeBase can help you patch your vulnerable systems to eliminate this bug and help you in situations where patching is not possible. We have a patented cyber security technique for exactly this situation. Learn more about our Dynamic Application Surveillance and Hardening feature.
Do not waste time! Secure your apps with MergeBase. You can try the MergeBase SCA tool to check if you are vulnerable or even download our free tool to detect vulnerable log4j versions on any of your machines and in any application.

