SCA+SAST+DAST+IAST+RASP+.. = JOY ?
spoiler alert: probably not
In this webinar, application security experts Jim Manico (OWASP top 10’s contributor), Farshad Abasi (OWASP Chapter Lead), and Julius Musseau will go over best practices for rolling out an effective Application Security Testing Toolset to your software development and security teams.
How can you best get started, and how can you best optimize your AppSec toolset over time?
Whether you are considering the implementing AppSec tools for the first time or aiming to enhance your existing toolset, understanding the key components and their functionalities is crucial. Application security specialists Jim Manico, Farshad Abasi, and Julius Musseau share valuable insights for deploying an effective AppSec toolset tailored to the unique needs of software development and security teams.
More specific:
1. What combination of tools gives you maximum protection?
2. What tool gives you the highest value out of the box?
3. How are threats likely to evolve, and how to use your AppSec tool set to stay one step ahead of cyber advisories?
How to select the perfect Application Security Testing Toolset?
Essential Components of Application Security Testing
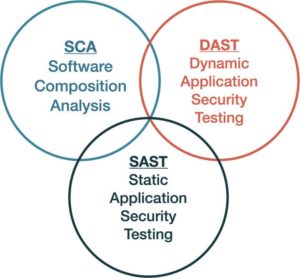
1. SAST – Static Application Security Testing It looks at the source code. The scanner will investigate the source code of the system, looking for bad coding practices. For example, static application security testing can spot SQL injection or hard-coded tokens and hard-coded passwords.
2. DAST – Dynamic Application Security Testing It looks at the running applications. If you have to running applications, perhaps production, a pilot, or a staging environment, the DAST tools enable you to detect security vulnerabilities in running applications using penetration tests.However, it tends to be a very slow process.
3. SCA – Software Composition Analysis (Third-Party Library Scanner) It is specifically about open source libraries. It looks at all the open source libraries in a software system. For example, protect your business against the Equifax attack or the log4j problem back in December 2021. In other words, It looks at bad software components and lets everyone know you need to upgrade; you need not.
The SCA tools are essential because open source reusable libraries are here to stay; everyone’s using them. MergeBase has research work about open source uses. The results show, for example, that Jira has around 80% at this point.
4. IAST – Interactive Application Security Testing It is about installing a runtime agent in the programming language, which is usually like the profiling or monitoring API of a core runtime engine and instrumentation API, and you will install an agent at the level of instrumentation to see how objects and classes and the like are executed by the runtime engine.
So you are installing an agent at the runtime level of the software and watching how the program runs, not from an external point of view, but from an agent that you have installed within the application itself. Get more visibility supposedly into how the app is running.
5. RASP – Runtime Application Self Protection It provides personalized protection to applications. provides real-time, tailored protection by leveraging the application’s own data and state. It identifies and isolates threats as they occur, enhancing the application’s resilience against attacks.
Matrix – Categorize Cybersecurity tools and Information Security Tools
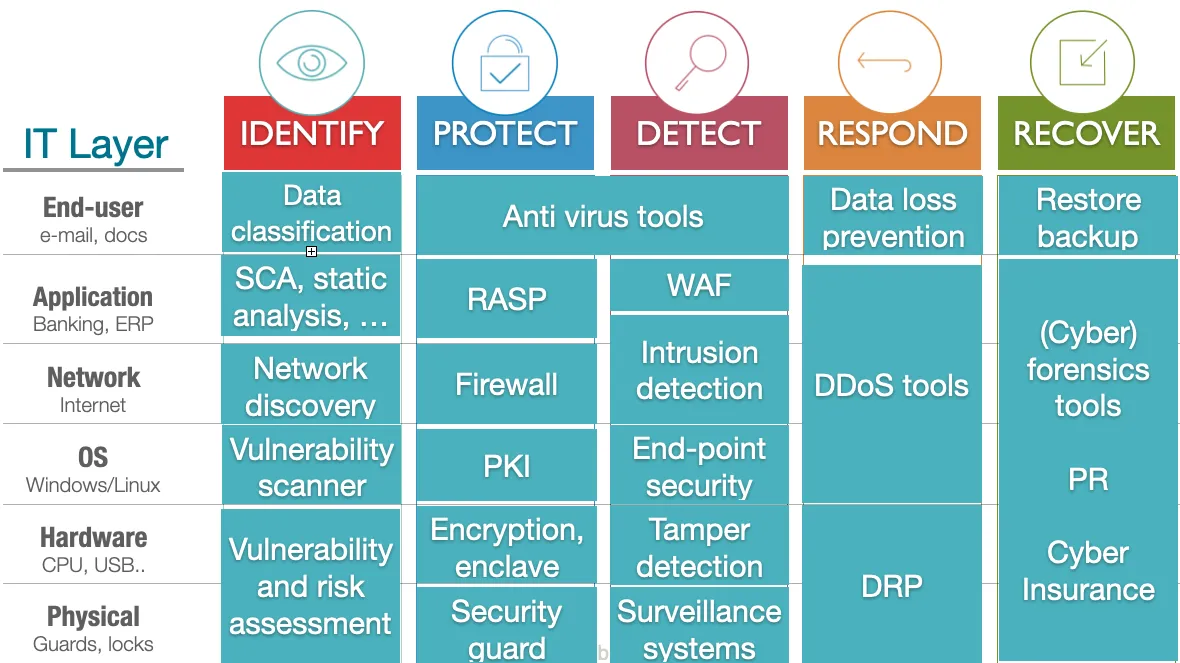
Application Security Toolset | Mergebase
What are common/typical challenges teams face when implementing these tools?
Implementing these tools is not without its challenges. Common issues include:
1. It lights up a lot of false positive number
2. It requires an expert operator.
Normally, they get flooded with findings right, like thousands of findings; what do you do, and how do you prioritize them? And the solution is to bring in an expert to tune.
Application Security Best Practices
Application Security Toolset
To effectively safeguard your applications, it is essential to adopt a multifaceted approach:
-
SCA – > External Libraries/ Supply Chain - Analyze applications for known vulnerabilities, and secure your software supply chain.
-
DAST – Test Application Surface - Try to break it into production applications. It will catch configuration issues and some of the above vulnerabilities.
-
SAST – Source code, developed in-house - Analyze source code to identify poor coding practices that could lead to security breaches.
These tools, when used in conjunction, provide a comprehensive shield against a wide array of security threats.
Securing Your Applications: Taking the Next Step
Securing your applications is an ongoing process that requires constant vigilance and adaptation to emerging threats. By understanding and effectively implementing the right mix of AppSec tools, you can significantly enhance the security of your software development lifecycle.
Take the first step towards comprehensive application security with MergeBase.

