The concept of Zero Trust (ZT) has been the source of hope and confusion for many organizations looking to improve and modernize their security strategies.
The concept is not new, but President Biden’s 2021 Executive Order has recently highlighted it. The order mentions ZT, Software Supply Chains, and SBOM as critical pieces toward better securing American institutions and people against cyber attacks.
Wide agreement exists that ZT concepts lead in a positive direction toward better security approaches. Implementing it requires fundamental changes and raises questions: How does it truly work? How do I apply it? What are the steps for its effective application? What are its broader implications?
In thos enlightening webinar, experts Jerry Hoff and Julius Musseau break down Zero Trust’s fundamental concepts, definitions, and implications. They also explore its intersection with application security, SBOM, and software supply chains.
Concept
Zero trust (ZT) is the term for an evolving set of cybersecurity paradigms that move defenses from static, network-based perimeters to focus on users, assets, and resources.
In other words, it challenges the traditional security model that relies on trusting entities inside the network and instead assumes that threats may already exist both inside and outside the network.
Definitions
ZT provides a collection of concepts and ideas designed to minimize uncertainty in enforcing accurate, least privileged per-request access decisions in information systems and services in the face of a network viewed as compromised.
Zero trust architecture (ZTA) is an enterprise’s cyber security plan that utilizes zero trust concepts and encompasses component relationships, workflow planning, and access policies.
Therefore, a ZT enterprise is the network infrastructure (physical and virtual) and operational policies that are in place for an enterprise as a product of a zero trust architecture plan.
Zero Trust | Mergebase
Source: NIST
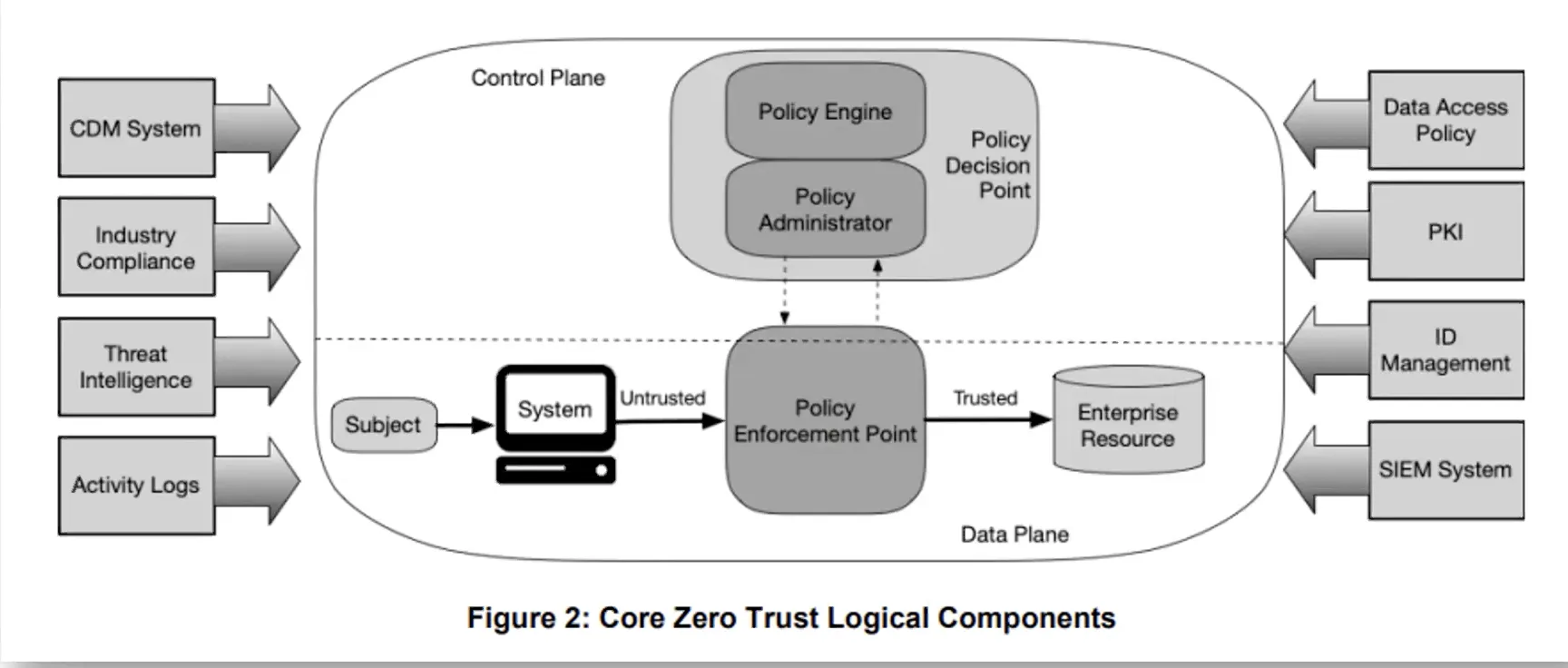
Core Zero Trust Logical Components
Zero Trust is underpinned by several critical elements, each contributing to its robustness and efficacy:
- Strong Authentication and Identity Management: Identity is the cornerstone of access control in Zero Trust.
- Identity-Based Access Control: Implementing stringent access controls for all connections, without exception.
- Encryption Across All Connections: Maintaining confidentiality and integrity of data in transit.
- Uniform Security Protocols: Consistently applying security rules across all environments, whether cloud-based or on-premises, and for both remote and in-house employees.
- Rigorous Device Management and Inspection: Controlling and monitoring devices that access the network.
- Strategic Access Granting and Governance: Methodical and well-governed access permissions.
- Comprehensive Monitoring: Continuously monitoring network activities for anomalies and potential threats.
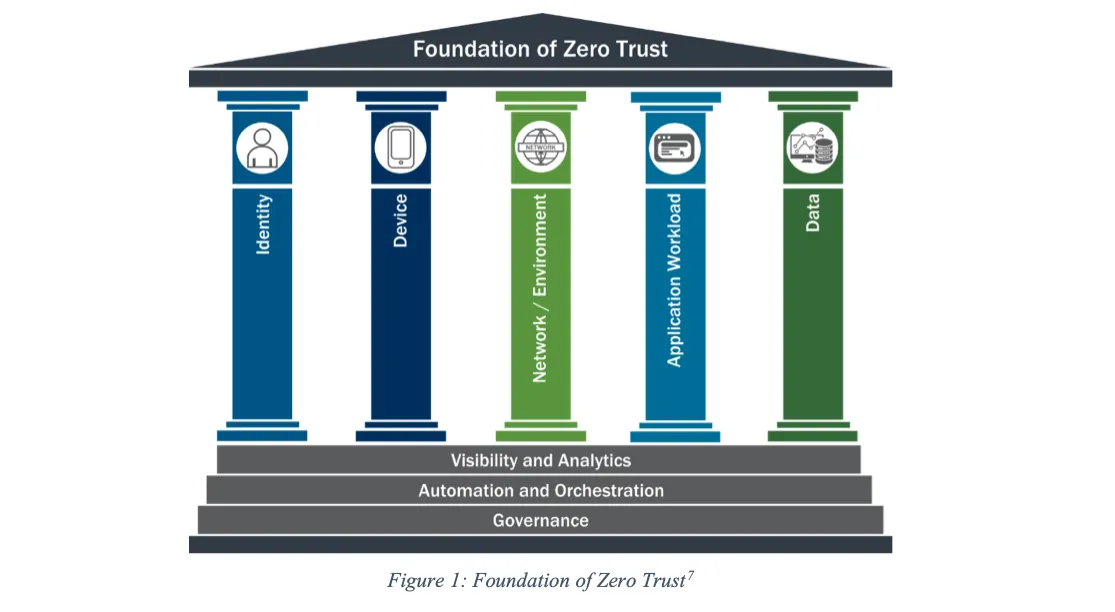
Base Pillars to build ZT
Zero Trust | Mergebase
Source: CISA
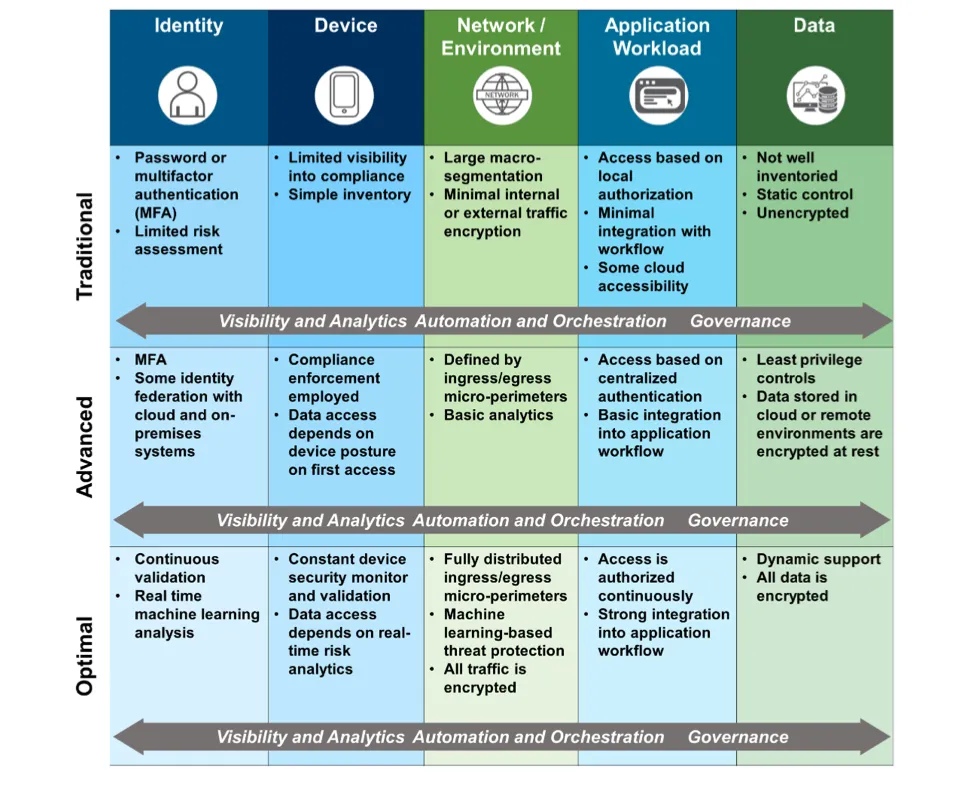
High-Level ZT Maturity Model
Zero Trust’s implementation can be evaluated using a high-level maturity model, comprising the following stages:
- Need for unified, centralized, overarching authentication
- Need for centralized authorization & decision-making capabilities
- Need for device information
- Updated SOC capabilities (EDR)
- Updated Training for Staff (design, implementation, deployment, production)
- Internal delegation (who oversees centralized auth, authz, etc…)
- Policy design, update, implementation (who?)
- Updated Governance (Many more decisions)
Zero Trust | Mergebase
Source: CISA
Implications for Application Security
Zero Trust has notable implications for application security, including a strong emphasis on identity management and breaking down the distinction between internally facing and externally facing systems.
Ensuring secure connections becomes pivotal, and ZT is increasingly associated with emerging application security regulations.
Exploring Zero Trust Security and Leveraging Mergebase for Enhanced Cybersecurity
To enhance the Zero Trust approach, organizations can significantly benefit from integrating Mergebase Software Composition Analysis (SCA) tool. Mergebase SCA enables comprehensive scanning and analysis of software components used in applications and systems.
By identifying vulnerabilities and risks associated with third-party and open-source software, Mergebase SCA helps organizations mitigate potential security threats and ensure the integrity of their software supply chains.
Integrating Mergebase SCA into the Zero Trust framework enhances the overall security posture and reduces the attack surface of the organization’s applications and systems.
Conclusion
Zero trust security is an emerging cybersecurity paradigm that enables businesses to protect their data and resources by verifying the identities of all users, devices, and applications before they’re given access.
In other words, with zero trust security, there are no trusted networks or users—everyone is treated the same, regardless of their past behaviour.
Ready to enhance your software security with Mergebase SCA?
Experience the benefits of comprehensive software composition analysis (SCA). Protect and fortify your software supply chain security with Mergebase’s free trial today.
FAQs
- What is Zero Trust?
- Zero Trust is a cybersecurity strategy focusing on stringent identity verification and assuming potential threats both inside and outside the network.
- How does Zero Trust enhance cybersecurity?
- It improves security by eliminating implicit trust and requiring continuous verification of every user and device attempting to access resources.
- What are the key components of Zero Trust?
- Key components include strong authentication, identity-based access control, encryption, consistent security rules application, and enriched monitoring.
- Why is Zero Trust important in modern cybersecurity?
- With increasing cyber threats and complex network environments, Zero Trust offers a more dynamic and secure approach to protecting resources and data.
- How can Mergebase SCA support Zero Trust?
- Mergebase SCA helps in identifying vulnerabilities in software components, enhancing the security posture within the Zero Trust framework.

