Welcome to the April edition of the MergeBase newsletter, your source for the latest updates and insights in the realm of software supply chain security. In this month’s issue, we bring you valuable information in our “Vulnerability Remediation Guide” and invite you to watch our live events focusing on reducing third-party risk proactively.
Company Live Events
Reduce 3rd-party Risk Proactively?
The complexity of third-party libraries makes them hard to analyze, leaving Java-based systems vulnerable to software supply chain attacks. With MergeBase SCA Runtime Protection you can reduce third-party risk by hardening applications against zero-day attacks. In this webinar appsec experts discuss the benefits of Java Runtime Protection, including identifying unused software, blocking unneeded Java libraries and functions, and reducing exposure to attackers.
Company News
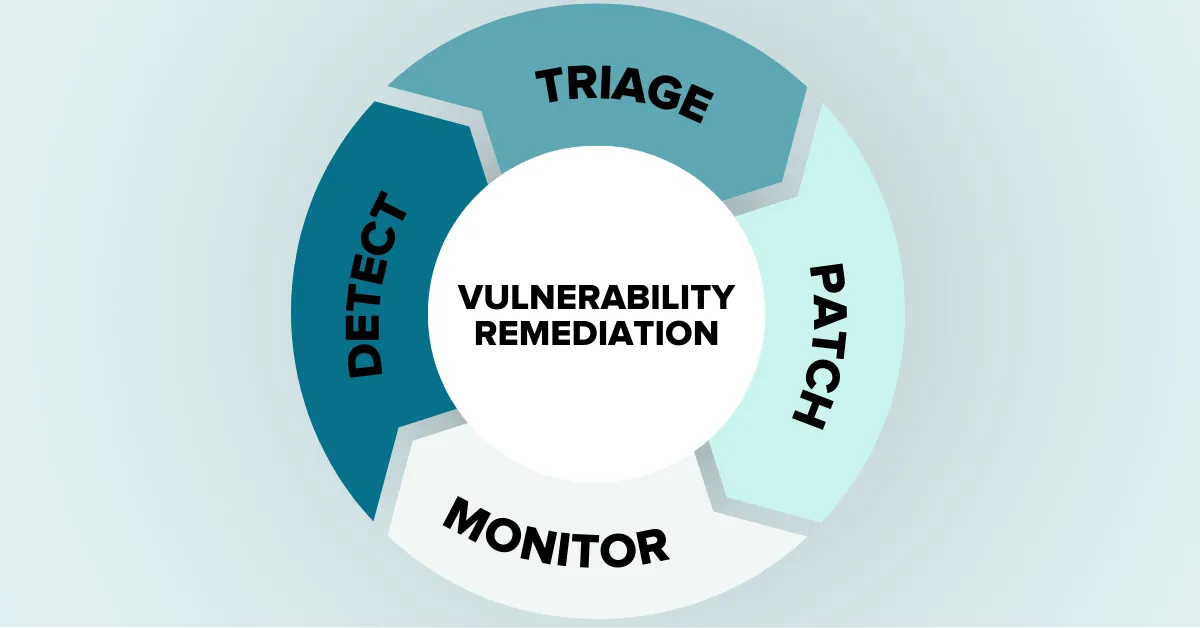
Vulnerability Remediation Guide
Vulnerability remediation is a critical process that helps find and fix security vulnerabilities in your systems. However, due to the complexities of large organizational systems and lack of resources, most codebases have known vulnerabilities in their runtime applications. This can lead to frustration and loss of morale among those responsible for keeping codebases safe. Our latest blog post provides valuable insights and best practices, along with how MergeBase’s SCA Runtime Protection can assist you to improve the security of your software systems. Check it now!
Ready for amazing customer service?
Our dedicated team of industry and product experts is well-versed in understanding your software supply chain security needs. We are committed to finding the right solution tailored to your unique requirements. Let’s work together to bolster your cybersecurity efforts.
How can we help you today?

