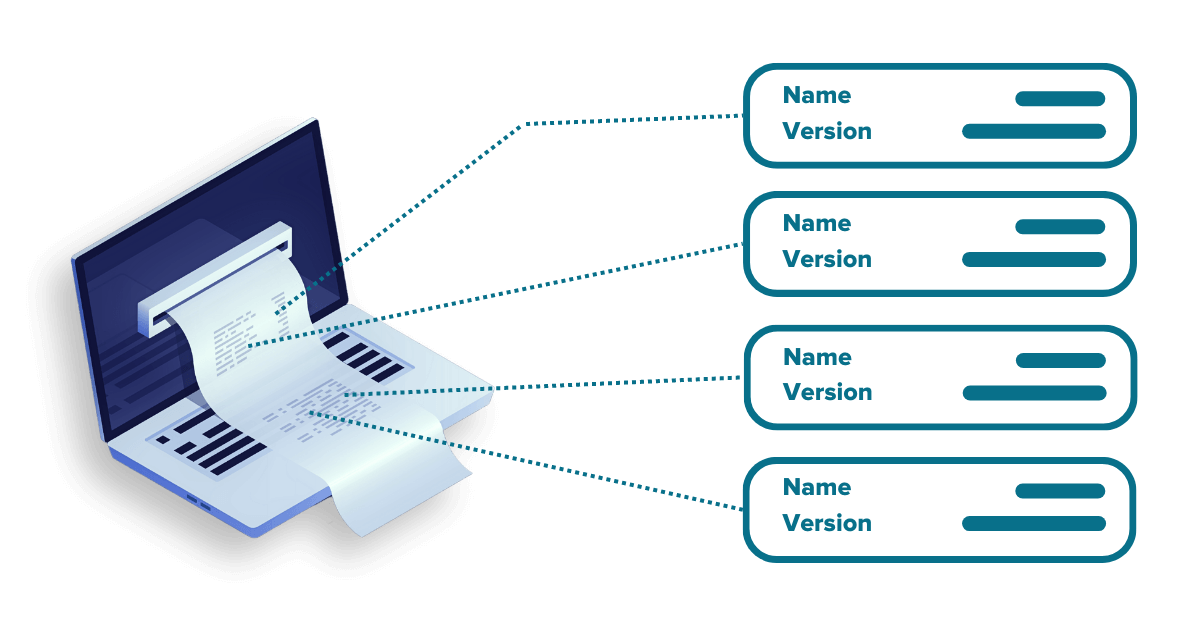
Reduce software supply chain risk with proven Software Composition Analysis (SCA).
Achieve compliance, secure applications, and reduce your organization’s supply chain attack surface with dynamic application surveillance and hardening and always-on software vulnerability management.
Get visibility to your software supply chain attack surface and stay ahead of adversaries. Keeping pace with rising cyber risk, ever-increasing vulnerabilities, and government-driven compliance requirements are complex, time consuming, and prone to error.